first of: A DRASTIC VIDEO:
JM Porup reports for Ars Technica:
The Linux kernel today faces an unprecedented safety crisis. Much like when Ralph Nader famously told the American public that their cars were “unsafe at any speed” back in 1965, numerous security developers told the 2016 Linux Security Summit in Toronto that the operating system needs a total rethink to keep it fit for purpose.
No longer the niche concern of years past, Linux today underpins the server farms that run the cloud, more than a billion Android phones, and not to mention the coming tsunami of grossly insecure devices that will be hitched to the Internet of Things. Today’s world runs on Linux, and the security of its kernel is a single point of failure that will affect the safety and well-being of almost every human being on the planet in one way or another.
“Cars were designed to run but not to fail,” Kees Cook, head of the Linux Kernel Self Protection Project, and a Google employee working on the future of IoT security, said at the summit. “Very comfortable while you’re going down the road, but as soon as you crashed, everybody died.”
“That’s not acceptable anymore,” he added, “and in a similar fashion the Linux kernel needs to deal with attacks in a manner where it actually is expecting them and actually handles gracefully in some fashion the fact that it’s being attacked.”
“That’s not acceptable anymore,” he added, “and in a similar fashion the Linux kernel needs to deal with attacks in a manner where it actually is expecting them and actually handles gracefully in some fashion the fact that it’s being attacked.”
Jeffrey Vander Stoep, a software engineer on the Android security team at Google, echoed Cook’s message: “This kind of hearkens back to last year’s keynote speech when [Konstantin “Kai” Ryabitsev] compared computer safety with the car industry years ago. We need more and we need better safety features, and with it in mind this may cause inconvenience for developers, we still need them.”
The clear consensus at the Linux Security Summit was that squashing bugs is a losing strategy. Many deployed devices running Linux will never receive security updates, and patching a security hole in the upstream kernel does nothing to ensure the safety of an IoT device that could be in use for a decade and may forever be ignored by the manufacturer.
Worse, the average lifetime of a critical security bug in the Linux kernel, from introduction during a code commit to public discovery and having a patch issued, averages three years or more.
Kernel drivers suck
However that’s hard to do when the vast majority of kernel bugs come from vendor drivers, not the upstream Linux kernel, Stoep said.
“Android does in fact inherit bugs from the upstream kernel,” he said, “but our data shows that most of Android’s kernel security vulnerabilities live in device drivers.”
src: https://www.infoworld.com/article/3124432/linux/is-the-linux-kernel-a-security-problem.html
okay first of all: Yes i also would like to have “as secure as possible” software/kernel on my servers.
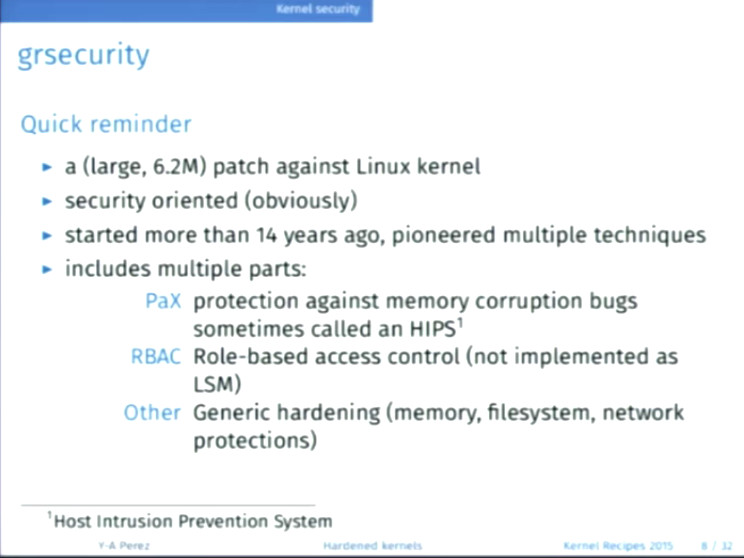
so what is the status of those grsecurity patches?
why are they not included into upstream kernel?
Thanks to Debian-Team and Yves, you can install it under Debian just like any other package… but ONLY! for Debian Jessie 8.0 not yet for Debian Stretch 9.0.
So it MIGHT be possible to install them under Debian Stretch 9.0 with jessie-backports?
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!