firewall & pinguin: iptables where do thou go?
it is said that when using “ip-sets” iptables and nftables achieve almost same performance (amounts of ips possible to block, without server becoming slow/unresponsive)
Redhat and nftables on DDoS “so the only thing to fall back to is establishing a blacklist for all the different source IP addresses” (src) (which is exactly what iptables + cron + autoban.sh a simple bash script does)
the #3rd concept: bpfilter
and: will already established iptables scripts keep on working?
“We like iptables after all, this tool has been serving us (and will likely keep serving still for a while in many deployments) to filter out traffic on both per-packet and per-flow basis, log suspicious traffic activity, perform NAT and many other things.
It comes with more than a hundred of extensions that have been contributed along the last 15 years!.
Nevertheless, the iptables framework suffers from limitations that cannot be easily worked around:
- Avoid code duplication and inconsistencies:
- Many of the iptables extensions are protocol specific
- so there is no a consolidated way to match packet fields
- instead there is one extension for each protocol that it supports
- this bloats the codebase with very similar code to perform a similar task: payload matching
- Faster packet classification through enhanced generic set and map infrastructure
- Simplified dual stack IPv4/IPv6 administration, through the new inet family that allows you to register base chains that see both IPv4 and IPv6 traffic
- Better dynamic ruleset updates support
- Provide a Netlink API for third party applications, just as other Linux Networking and Netfilter subsystem do
- Address syntax inconsistencies and provide nicer and more compact syntax (aha aha X-D)
These, among other things not listed here, triggered the nftables development which was originally presented to the Netfilter community in the 6th Netfilter Workshop in Paris (2008, France).” (src: wiki.nftables.org)
if fail2ban fails to ban, when nftables is used to emulate iptables
it’s not entirely nftables’ fault, fail2ban would need to support it, so if you do not need to block more than 50-100.000 IPs and have a reasonable fast server… it should not slow down with iptables.
CentOS7 uninstall nftables install iptables – what to expect for Debian 11
https://dwaves.de/2017/07/27/centos7-replaced-firewall-iptables-with-firewalld-iptables-vs-nftables-benchmark-performance-comparison-scalability-when-facing-ddos-scenarios/
list all jails
fail2ban-client status
Status
|- Number of jail: 1
`- Jail list: sshd
get status:
/scripts/fail2ban_status.sh
echo "===== fail2ban status ====="
JAILS=`fail2ban-client status | grep "Jail list" | sed -E 's/^[^:]+:[ \t]+//' | sed 's/,//g'`
for JAIL in $JAILS
do
fail2ban-client status $JAIL
done
fail2ban-client status sshd
fail2ban-client status
systemctl status fail2ban
echo "===== iptables status ====="
iptables -S|grep "REJECT"
echo "===== showing all available filters ====="
ll /etc/fail2ban/filter.d/
journalctl -b -u fail2ban
echo "===== fail2ban log ====="
tail /var/log/fail2ban.log
unban this ip:
unban:
/scripts/fail2ban_unban.sh 123.123.123.123
#!/bin/bash
echo "====== unbanning:" $1
JAILS=`fail2ban-client status | grep "Jail list" | sed -E 's/^[^:]+:[ \t]+//' | sed 's/,//g'`
for JAIL in $JAILS
do
fail2ban-client set $JAIL unbanip $1;
done
manually ban an ip:
/scripts/fail2ban_ban.sh 123.123.123.123
#!/bin/bash
echo "====== banning:" $1
JAILS=`fail2ban-client status | grep "Jail list" | sed -E 's/^[^:]+:[ \t]+//' | sed 's/,//g'`
for JAIL in $JAILS
do
fail2ban-client set $JAIL banip $1;
done
automatically ban by sshd logging to /var/log/secure
think fail2ban is to soft on hosts that try to brute force your password?
run this via hourly cron X-D
this is a small script one put together, which will filter out all “Invalid user” and “preauth” from /var/log/secure and ban the ips associated.
#!/bin/bash
# this script will take ssh messages logged to /var/log/secure
# extract two kinds of ips:
# 1) "Invalid user"
# 2) "preauth"
# and block them via fail2ban
# reduce to
# filter out "Invalid user" and "preauth" and save it to new file
NEWFILE="/var/log/secure_invalid_preauth.log"
cat /var/log/secure | grep -e "Invalid user" -e "preauth" > $NEWFILE
# extract ips
octet='\<(25[0-5]|2[0-4][0-9]|1[0-9][0-9]|[1-9][0-9]?)\>'
ip="$octet\\.$octet\\.$octet\\.$octet"
# also remove duplicates
# save to new file log2
grep -Eo "$ip" $NEWFILE | paste - | uniq > $NEWFILE"2"
# iterate over every line of a file and
while read line; do
echo "this was a very bad host, we will ban it now:"
echo "$line"
fail2ban-client set sshd banip $line;
done <$NEWFILE"2"
echo "done"
how often was jail enforced?
fail2ban-client status sshd
Status for the jail: sshd
|- Filter
| |- Currently failed: 1
| |- Total failed: 1779
| `- Journal matches: _SYSTEMD_UNIT=sshd.service + _COMM=sshd
`- Actions
|- Currently banned: 1
|- Total banned: 347
`- Banned IP list: 212.129.140.74
what ip got banned most?
awk '($(NF-1) = /Ban/){print $NF}' /var/log/fail2ban.log | sort | uniq -c | sort -n
1 125.163.71.XXX
1 37.75.213.XXX
1 80.199.0.XXX
2 151.236.200.XXX
2 190.85.234.XXX
4 188.75.155.XXX
4 190.223.32.XXX
4 200.105.154.XXX
6 191.209.9.XXX
11 78.250.49.XXX
34 176.223.165.XXX
133 104.236.146.XXX
174 103.72.162.XXX
184 54.37.196.XXX
what subnets got banned most?
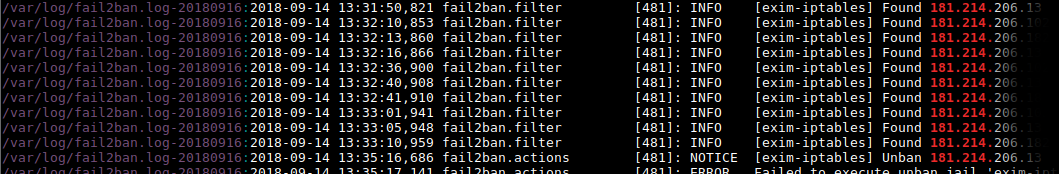
zgrep -h "Ban " /var/log/fail2ban.log* | awk '{print $NF}' | awk -F\. '{print $1"."$2"."}' | sort | uniq -c | sort -n | tail # those subnets got banned most (higher number = more bans) 17 200.105. 21 210.92. 23 27.255. 34 176.223. 93 45.125. 140 104.236. 175 103.72. 184 54.37. 226 200.111. 1190 181.214. # this e.g. is an ip from malaysia that exceeded fail2ban rules for exim a lot whois 103.72.162.186 # show ips of the most banned subnet 181.214. grep -r -i -E --color=auto "181.214." /var/log/fail2ban*;
… i whoised 3 and all were in fail2ban jail for exim-iptables, all were US located and attempts to use this server for spam?
address: 60007 – Chicago – IL
country: US
Links:
https://www.the-art-of-web.com/system/fail2ban-log/
Links:
credits: https://gist.github.com/kamermans/1076290
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!