Pwn2Own 2020: opening a pdf can be enough to compromise system!
https://youtu.be/u1udr7j9MQA?t=359
90% of companies DO NOT NEED JavaScript or macros to run in PDF
but still it is there… and Adobe knows about it:
“JavaScripts in PDFs as a security risk”
src: https://helpx.adobe.com/acrobat/using/javascripts-pdfs-security-risk.html
EMOTET is coming via encpryted (!) PDF files undtected by AntiVirus scanners.
The question is: If Adobe knows it is dangerous – Why is JavaScript not disabled per default on Adobe Reader?
First of all update one’s Adobe Reader to latest available version…
https://www.chip.de/downloads/Adobe-Acrobat-Reader-DC_12998358.html
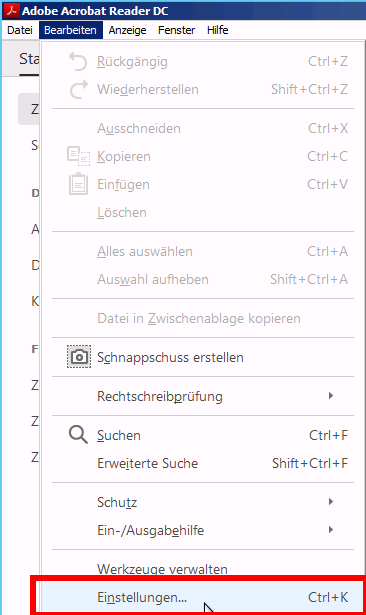
How to disable JavaScript in PDFs:
Acrobat and Acrobat Reader let you adjust application behavior so that JavaScript executes within your desired level of security. This helps restrict application access to JavaScript APIs and isolates workflows that do not require JavaScript APIs.
- Choose Edit > Preferences (Windows) or Acrobat / Acrobat Reader > Preferences (Mac OS).
- From the Categories on the left, select JavaScript.
- In the JavaScript Security panel, set options to manage JavaScript: as needed
- uncheck to disable JavaScript completely or restrict JavaScript through APIs.
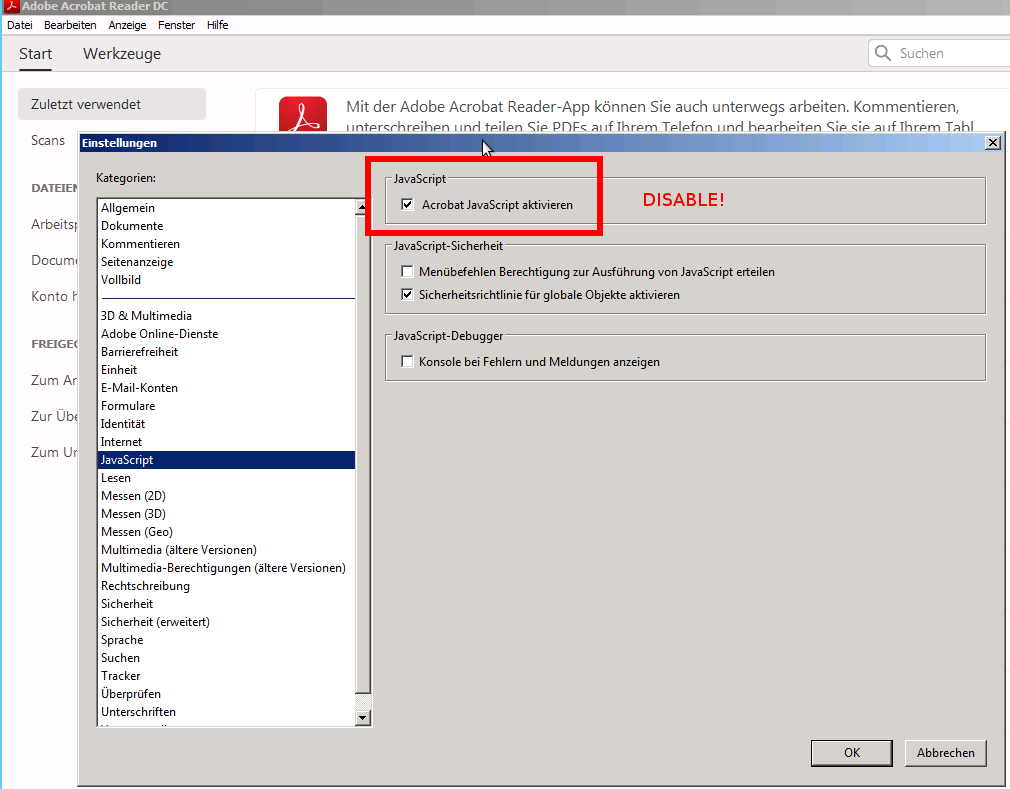
Protected mode
nobody knows how protected one is with protected mode… and what it actually does?
“By default, Adobe Reader DC runs in protected mode to provide an added layer of security.
In protected mode, malicious PDF documents can’t launch arbitrary executable files or write to system directories or the Windows Registry.
To check the status of protected mode, choose File > Properties > Advanced > Protected Mode.
Protected mode is enabled by default. To specify the settings, do the following:
- Choose Edit > Preferences
- n the Categories list on the left, select Security (Enhanced)
- click View Log to open the log file.In the Sandbox Protections section, select or deselect Enable Protected Mode At Startup.
- Enable Create Protected Mode Log File to record events. The changes take effect the next time you start the application.”
https://helpx.adobe.com/reader/using/protected-mode-windows.html
-
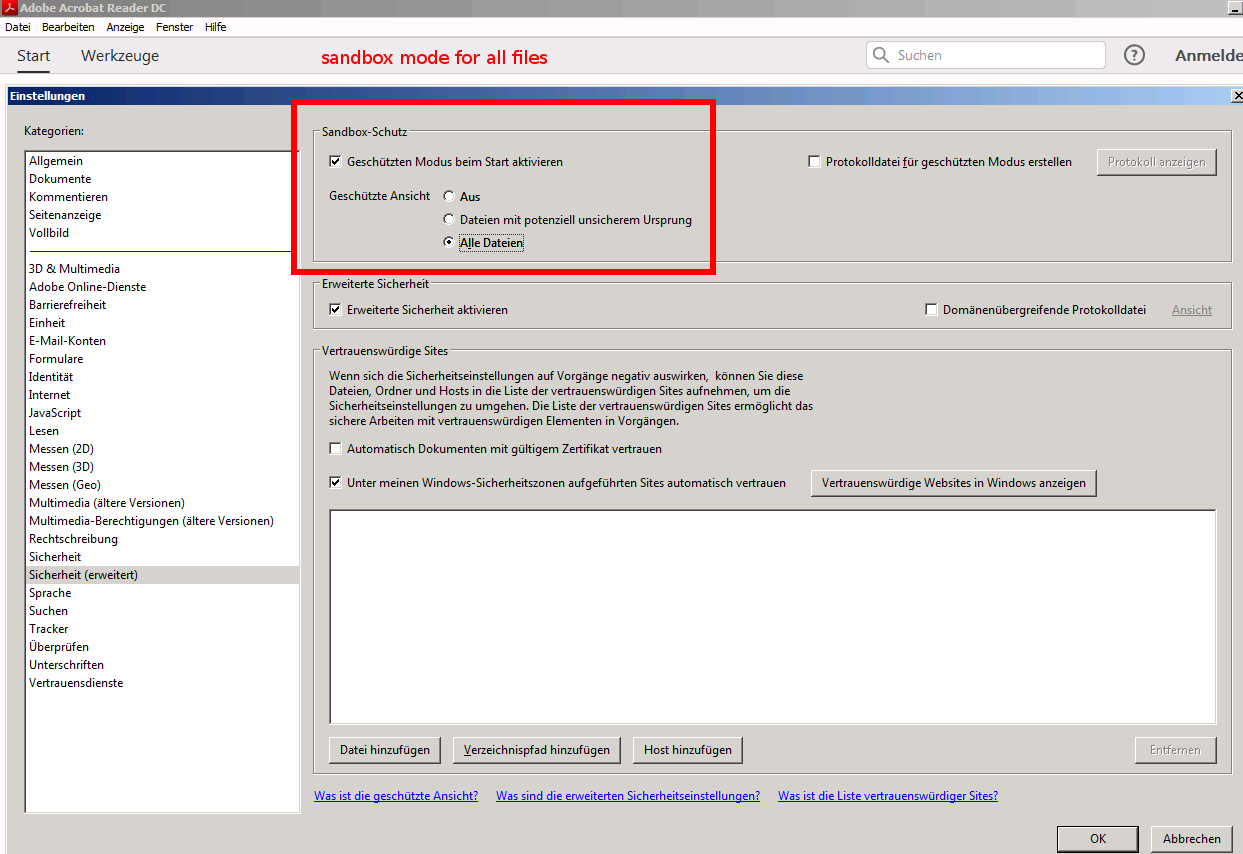
Adobe Reader Sandbox?
how effective this sandbox is… nobody knows…
https://duckduckgo.com/?q=Adobe+Reader+Sandbox&t=ffab&ia=web
Sandboxing is a technique developers use to create a confined execution environment for running untrusted programs.
In the context of Acrobat products, an “untrusted program” is any PDF and the processes it invokes.
By default, the product assumes any PDF is potentially malicious and confines all processing to a sandbox.
Sandboxes are typically used when data (such as documents or executable code) arrives from an untrusted source.
A sandbox limits, or reduces, the level of access its applications have.
For example, creating and executing files and modifying system information such as certain registry settings and other control panel functions are prohibited.
If a process P runs a child process Q in a sandbox, then Q’s privileges would typically be restricted to a subset of P’s.
For example, if P is running on a system, then P may be able to look at all processes on the system.
Q, however, will only be able to look at processes that are in the same sandbox as Q.
Barring any vulnerabilities in the sandbox mechanism itself, the scope of potential damage caused by a misbehaving Q is reduced.
src: https://www.adobe.com/devnet-docs/acrobatetk/tools/AppSec/sandboxprotections.html
Links:
For details, see the Application Security Guide at www.adobe.com/go/learn_acr_appsecurity_en.
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!